Anti-virus for Mac for PCI Compliance
When a contract requires anti-virus on all computers, even the Mac OS X systems, which do you choose?
Macs are not Commonly Affected, in the traditional sense
One nice thing about working in a heavily Mac OS X environment, which most Ruby on Rails development companies are is that there just are not the number and variety of viruses on the platform as there are in the Windows environment.
This is not to say that a Mac user does not face many security threats - they do face threats, nor that they cannot be hacked - they most certainly can be hacked. In fact, a review of Secunia’s Vulnerability Report: Apple Macintosh OS X is a good exercise here. All this said, Macs are just not commonly known to be affected by viruses in the same sense that a Windows or DOS computer has been. And some of this is the economics of virus authoring.
However, as a Mac OS X user, I am not invulnerable and I am still required by contract to install and use anti-virus software.
The PCI Requirement
Everyone who has had to deal with a company accepting credit card transactions knows about the Payment Card Industry Digital Security Standards (PCI-DSS). You can read the rules for yourself at Payment Card Industry (PCI) Data Security Standard: Requirements and Security Assessment Procedures - Version 2.0 (PDF document). It’s 75 pages long, and in my personal opinion is great light bedtime reading. Among its requirements is that all companies that handle credit card data in anyway, even just keying it into a web-based terminal, must maintain an vulnerability management program. This prescriptively requires that the business must:
- Requirement 5: Use and regularly update anti-virus software or programs
- Requirement 6: Develop and maintain secure systems and applications
In this post, I am focusing in an Requirement 5, which declares that the company must (as in not optional):
- Deploy anti-virus software on all systems commonly affected by malicious software (particularly personal computers and servers).
- Ensure that all anti-virus programs are capable of detecting, removing, and protecting against all known types of malicious software.
- Ensure that all anti-virus mechanisms are current, actively running, and generating audit logs.
- That such logs provide an audit trail history that is retained for at least one year, with a minimum of three months immediately available for analysis (for example, online, archived, or restorable from back-up).
And yes, they will check on this. At the very least with a detailed assessment questionnaire that the company owner will sign or via actual audit.
But, what if we do not store any credit card numbers
For any business, one of the most important security precautions is to never store credit card numbers - not ever. Using a gateway service with payment data tokenization, such as Stripe, BluePay, or even Authorize.net’s CIM is vital.
It is best if your business never touches any customer credit card details, but such details are only ever entered by customers directly. However, if you ever take card details from a customer, such as over the phone, and then type that data into your invoicing software or merchant virtual terminal, then you have to pay attention to PCI-DSS.
That last case is the situation that my own company is in. We do not handle a lot of credit cards, not like a brick and mortar merchant would. Therefore, we still have to take contractually mandated security precautions.
In light of this requirement, choosing a good anti-virus
At this stage, you are looking for an anti-virus provider that:
- Runs on Mac OS X
- Is capable of detecting known threats
- Automatically updates virus definitions and its scanning engine
- Compiles a detailed log that is auditable and is maintained for at least a year.
Next, I am going to review the two products that I am currently using in my own company. This is not meant to be a side-by-side guide of all products on the market with pros and cons of each. Feel free to research your options based upon these criteria to find out what’s best for your company.
Trend Micro Titanium
Last year, I took a look at several anti-virus applications, and ended up settling on Trend Micro Titanium for Mac OS X for my own systems. This is not to say that it is only option, but it has an inexpensive annual subscription and checks off all of the requirements.
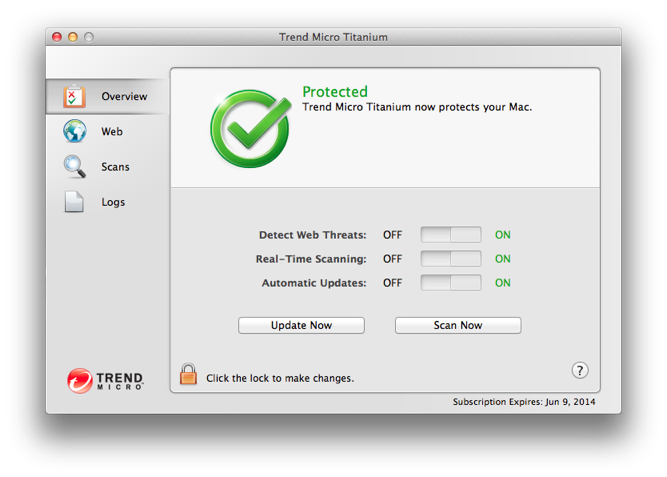
Automatic Detection and Updates
Once installed it can be configured to automatically detect known threats and update.
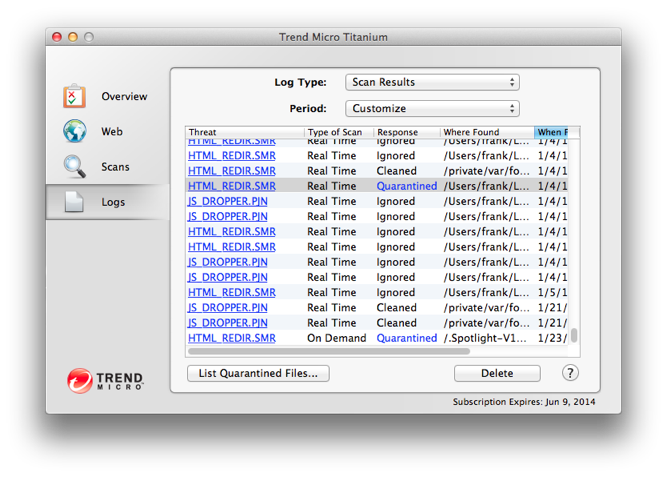
Sufficient Logging for the Audit Requirement
It keeps a sufficient log, and by using the Customize filter, you can go back for a year or more. Be sure not to click the Delete button, which clears out the logs though.
As a Bonus, Content Filtering for the Web
For my own systems, I like to set up parental filters for myself to make it harder for me to stumble upon websites that may be potentially dangerous or simply not-safe-for-work. This is easy to do with Titanium by starting with the stock Mature Teenager filter and then customizing it as needed:
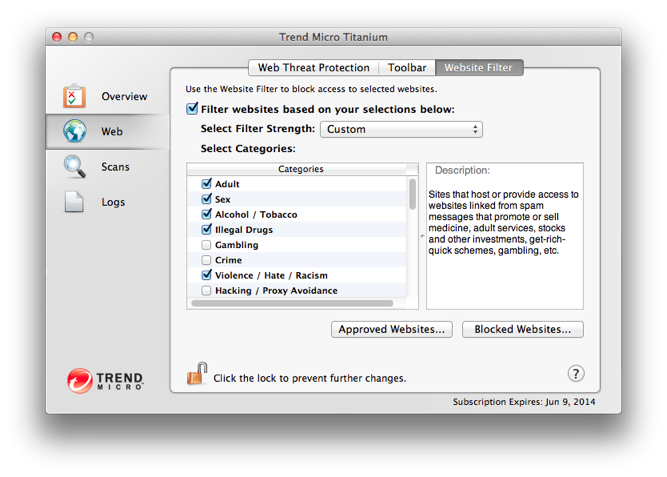
This is not strictly a PCI requirement, but is a good part of an information security program.
Effectiveness
In practice, I have found Trend Micro Titanium effective at detecting malicious file attachments in email messages and blocking questionable websites. It does a good job detecting malicious JavaScripts, which do in fact run on any web browser to attempt cross-site scripting attacks. For this alone, it is a worthwhile security tool for a professional using a Apple computer for work.
ClamAV
ClamAV is an open source anti-virus platform that is very popular for use on servers that is available at http://www.clamav.net/. It normally runs as a command line tool and I like to install in through Homebrew on Mac OS X systems. If you are on Linux, then this is certainly available through your package manager. It has an automatic update daemon called freshclam and can be scripted to your hearts content.
It’s really good and it really is more for a programmer or system administrator to setup.
For a version with a graphical user interface, see http://www.clamxav.com.
In Conclusion
ClamAV is a wonderfully flexible anti-virus platform, but getting it setup is involved. For my company, Trend Micro Titanium is a good overall anti-virus that is inexpensive, was on sale for $19.95/year/Mac at the time of this writing, and appears to satisfy the PCI-DSS contract requirements for occasionally interacting with clients’ credit card numbers.
As a Matter of Policy
Anti-virus is one technical control that is implemented as part of a vulnerability management program, that is an important part of a comprehensive information security program. Your program should be multi-faceted with the aim of providing defense in depth and documented with a written information security policy.
This is not Specific Advice
If you need to be PCI compliant, then know that there are many additional requirements that are beyond the scope of this blog post. This post is meant to be a general discussion of important topics and is not offered as legal or security consulting advice. The author is a security professional, but is not himself a PCI assessor.
